Security
Tag Cloud: Security
A
Feb 27, 2026 AI & Intelligence
ALERT: 800+ Malicious Plugins Found in ClawHub Skill Library — Is Your API Key Safe?
Feb 27, 2026 AI & Intelligence
ALERT: 800+ Malicious Plugins Found in ClawHub Skill Library — Is Your API Key Safe?
F
Feb 26, 2026 AI & Intelligence
From Beginner to Pro: 5 Critical Security Settings You Can't Ignore in OpenClaw Initial Configuration

Feb 26, 2026 AI & Intelligence
From Beginner to Pro: 5 Critical Security Settings You Can't Ignore in OpenClaw Initial Configuration
O
Feb 5, 2026 AI & Intelligence
OpenClaw Skill Security Review: A 5-Minute Practical Guide to Identifying Malicious AgentSkills
Feb 5, 2026 AI & Intelligence
OpenClaw Skill Security Review: A 5-Minute Practical Guide to Identifying Malicious AgentSkills
O
Feb 4, 2026 AI & Intelligence
OpenClaw Security Configuration Guide: Five-Layer Defense from Docker Sandbox to Access Control

Feb 4, 2026 AI & Intelligence
OpenClaw Security Configuration Guide: Five-Layer Defense from Docker Sandbox to Access Control
N
Jan 7, 2026 Technology
Next.js Admin Panel in Practice: Complete Guide to RBAC Permission System Design and Implementation

Jan 7, 2026 Technology
Next.js Admin Panel in Practice: Complete Guide to RBAC Permission System Design and Implementation
N
Jan 5, 2026 Technology
Next.js API Authentication & Security: A Complete Guide from JWT to Rate Limiting

Jan 5, 2026 Technology
Next.js API Authentication & Security: A Complete Guide from JWT to Rate Limiting
C
Dec 19, 2025 Technology
Complete Guide to OAuth Login in Next.js: Configuring Google, GitHub, and WeChat Authentication

Dec 19, 2025 Technology
Complete Guide to OAuth Login in Next.js: Configuring Google, GitHub, and WeChat Authentication
N
Dec 19, 2025 Technology
Next.js Route Protection & Authorization: Complete Guide to Middleware and Multi-Layer Defense
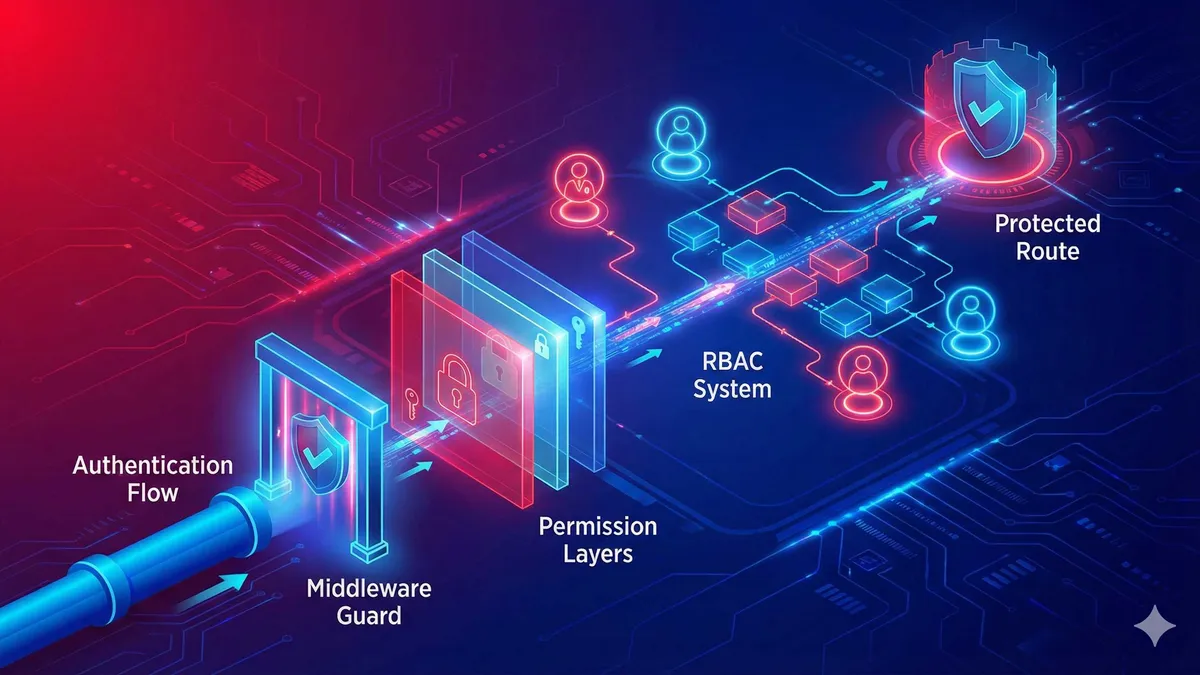
Dec 19, 2025 Technology
Next.js Route Protection & Authorization: Complete Guide to Middleware and Multi-Layer Defense
I
Dec 19, 2025 Technology
Implementing OAuth Login in Next.js: A Hands-On Guide to Google, GitHub, and WeChat Integration

Dec 19, 2025 Technology
Implementing OAuth Login in Next.js: A Hands-On Guide to Google, GitHub, and WeChat Integration
D
Dec 18, 2025 Technology
Docker Security Best Practices: Stop Running Containers as Root
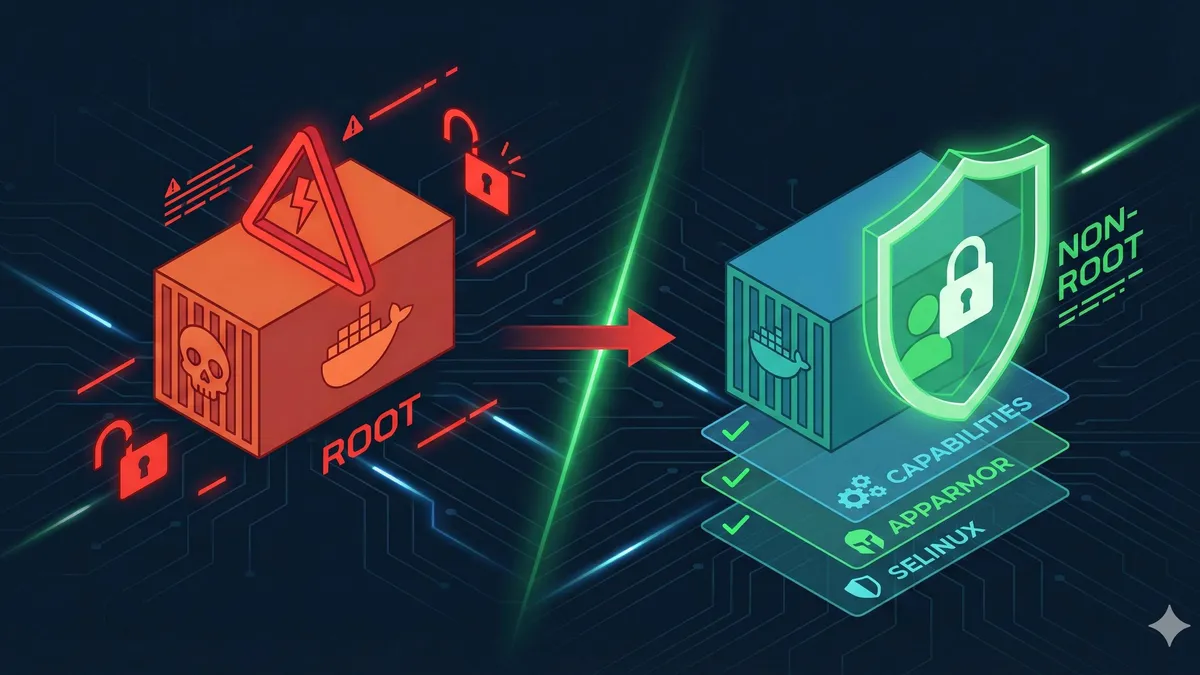
Dec 18, 2025 Technology
Docker Security Best Practices: Stop Running Containers as Root
T
Dec 18, 2025 Technology
The Complete Guide to Docker Secrets: Best Practices for Securely Managing Container Passwords and API Keys

Dec 18, 2025 Technology
The Complete Guide to Docker Secrets: Best Practices for Securely Managing Container Passwords and API Keys
D
Dec 18, 2025 Technology
Docker Image Security Scanning and Vulnerability Remediation: Trivy Tutorial and CI/CD Integration Guide
Dec 18, 2025 Technology
